Electronic warfare evolves to meet new threats
U.S. military feels pressure to keep its technological lead in a never-ending battle for the electromagnetic spectrum.
BY J.R. Wilson
"All war is based on deception." - Sun Tzu
The weapons and technologies of war are constantly evolving - changing more rapidly year to year in the 21st Century than they did century to century when Chinese general Sun Tzu wrote The Art of War some 2,500 years ago. Yet Sun Tzu's writings remain central guidelines even today; the need to control the high ground is applicable to one of the most advanced and increasingly critical realms of modern combat: electronic warfare (EW).
"Spectrum dominance is the new high ground; all weapons systems today are highly reliant on communications of one sort or another, whether global positioning system (GPS) or internal communications. If someone can distort GPS or disable onboard systems, you're toast," says Bob Schena, CEO of Rajant Corp. in Malvern, Pa. "On a scale of 1 to 10, it's a 12. We are so reliant on communications in our style of fighting that it is absolutely critical and will get even more critical. If you're at a communications disadvantage, I don't see how you can last very long."
EW itself is changing as well, with the lines between EW, cyber warfare, and signals intelligence (SIGINT) tending to blur in the heat of battle.
"We call it Spectrum Operations, which touches every type of operation - combat, humanitarian, etc.," notes U.S. Marine Corps Col. Gregory Breazile, director of the Marine Corps Information Warfare Integration Division at Quantico Marine Base, Va. "Spectrum is a physical means we use to support our operations, from sensing adversaries to supporting our own operational capabilities. We debated whether to call it Spectrum Warfare, but that was determined to be somewhat limiting, while Spectrum Ops better covered it all.
"We've also debated about whether spectrum should be another domain of warfighting," Breazile continues. "When we talk about 5th generation warfare, it really is spectrum that is the physical means where we will deliver effects on the battlefield that are different from what we've done in the past. I think that debate will continue and in the future we may see spectrum declared an operational domain. Nothing we've done in the past will resemble what we will do employing EW in the future, using multifunctional capabilities for sensing, attack, and force protection."
A similar reconfiguration is under- way in the U.S. Army, says Maj. Rich-ard Michel, Cyber & EW Operations Troop Commander within the Army's Asymmetric Warfare Group (AWG) at Fort Meade, Md. "As a result of our better understanding of multi-domain battle and our use of EW, cyber, and space ops as they continue to evolve, we will continue to experience a more advanced and capable Army than has ever been seen in history," Michel says. "AWG's job is to look at the decision-making process, how that will change doctrine and organizations. New technologies give commanders better options on how to employ that capability. That is an inevitability and an absolute positive for the Army, with greater capabilities and technologies empowering us to accomplish our goals.
"The force today is drastically different from what it was 10 years ago. Advances in EW enable a commander to make decisions he never had 50 years ago. In the past, a commander may have had no choice but to allow an adversary to use a specific asset or to destroy that asset. EW gives that commander other options, such as degrading or disabling an asset for a period of time."
"Just as water retains no constant shape, so in warfare there are no constant conditions. He who can modify his tactics in relation to his opponent and thereby succeed in winning may be called a heaven-born captain." - Sun Tzu
While others maintain EW is not, and probably never will be, declared a full and independent domain of war - joining air, land, sea, space, and cyber - Kent Snyder, vice president of Sierra Nevada Corp. in Sparks, Nev., says he has a different perspective.
"Going from an asymmetric fight and limited capability adversary in an austere environment to a peer or near-peer fight changes the paradigm. The EW fight now is being looked at in a more traditional sense of full-spectrum military operations, making it an integral part of how we fight, where before it was more an appended capability. EW is becoming as critical as a domain of battle as air, sea, and land and is gaining parity with those actual domains of battle," Snyder says.
"How EW will change the battlefield is growing and we must move as aggressively as possible to improve our fielded capabilities," Snyder continues. "The capability that is integrated into military forces worldwide will be the most relevant. With respect to EW, it is the military force spun up to integrate into its various formations that will provide a decisive advantage on the battlefield. Obviously Russia and China are the other key players, but there are a lot of others out there."
Some of the key technologies that are either already part of deployed EW capabilities, soon will be, or are targets include:
- digital signal processing;
- high-performance, small-form factor embedded computing;
- advanced algorithms;
- RF and microwave transceivers and components;
- electronics miniaturization;
- digitally programmable radar and communications;
- jammers and anti-jammers;
- GPS and companion/replacement location/navigation systems; and
- counter-measures to the counter-measures.
"We provide oversight over the acquisition of capabilities we require. When we write require- ments, we give them to the Marine Corps acquisition arm," Breazile explains. "As part of that process, we also are tied into the S&T [science and technology] world and communicate with industry so we understand what is out there. We want to be well-informed about future capabilities."
Gap-filling technologies
"We write joint concepts about the future operating environment and where we want to be in the next 10 years, keeping in mind where we think technology will lead us, then deconstruct that down to the capabilities required to operate in those future environments. Then we look to see where we have gaps and go to industry to find technologies to fill those gaps," Breazile says.
There are several similarities between the Marine Corps IWID and the Army's AWG, which was established in 2006 to enhance soldier survivability against the improvised explosive device (IED) threat in Southwest Asia. Today, the organization's primary focus is Cross-Domain Maneuver within Multi-Domain Battle, which replaced the Army's long-time Air-Land Battle approach. Yet the Army's Michel says technology is not AWG's true focus.
"AWG is involved in identifying threats regardless of source," Michel explains. "The operational environment we face today is certainly more complex than ever before in history. And as the environment changes, so do techniques and technologies. We bring that back to the Army for much larger strategic decisions on how the Army will counter those threats. AWG affects the tactical level, but informs the strategic level.
"Part of our solution development process is to make observations and on-the-spot recommendations, but also bring those observations back to the Concepts and Integration Squadron within AWG, which thinks in broader terms about developing concepts to identify larger or better solutions, then how to take that to TRADOC [Training & Doctrine Command] or the Centers of Excellence with recommendations on how they might make changes to meet current or perceived threats."
They also assist with Doctrine, Organization, Training, Materiel, Leadership and Education, Personnel, Facilities, and Policy - otherwise known as DOTMLPF-P.
"We're not just looking at equipment, but the personnel, the doctrine, the policies, the organization, and training facilities for EW to develop a rapid, capable solution. Identifying future threats is part of AWG's job - if this is the current threat, what recommendations do we have to counter that threat, then what will the enemy do to counter our counter?" Michel adds.
"We want to be proactive, not reactive. Given our current threat environment, the development of EW technologies is absolutely essential to the success of the Army in the future. But we're not solely dependent on changes in technology; we also rely on the adaptability of our soldiers. Technology is just a piece of that. If the EW capability exists in a way you've never experienced before, you will find new ways to use it," Michel says.
"The clever combatant imposes his will on the enemy, but does not allow the enemy's will to be imposed on him." - Sun Tzu
"In defensive EW, you're trying to stop signals from affecting you; offensive EW is pushing your signals out to affect others," says Sierra Nevada's Snyder. "It's the same spectrum, just different applications of how you use the technology. With a true multifunction capability and simultaneity of effect, you can do both at the same time from the same device. EW is a critical win/no-win requirement. If you can maintain the integrity of your spectral capability and the enemy can't penetrate it, then you will dominate the battlefield."
For industry, technology is the key to developing advanced, cutting-edge EW capabilities, but they also must be cognizant of the military's multifaceted requirements - greatly improved size, weight, and power (SWaP), cross-service commonality, modularity, minimal training and maintenance, and the ability of EW systems to defend themselves against EW counter attacks.
Coming to the table in new or improved capabilities are several sensors on one platform; fast on-board processing of ever-growing amounts of raw data; onboard data fusion; command-and-control modules that can react to a new threat without waiting for ground station commands; longer unmanned aerial vehicle (UAV) ranges and loiter times; SWaP-C (SWaP plus cost) improvements at every level; and a close connection with commercial manufacturers to identify, adopt, and adapt new technologies for military applications.
As with nearly every other aspect of technology, the military has come to depend on all that is coming out of the commercial world, but put into extreme conditions, says Marc Couture, senior product manager for digital signal processing at the Curtiss-Wright Corp. Defense Solutions Division in Ashburn, Va.
"In EW, you need to convert everything to ones and zeros with analog-to-digital converters. In terms of capturing the EM spectrum in an RF microwave sense, we have some products that capture data at 25 gigasamples per second, which is a huge amount and fairly unique," Couture says; 1 gigasample is one billion samples. "What's been very instrumental with the A/D converters is the speed of gigasamples per second is getting faster and faster and with greater resolution.
"With an EW system, then, you can keep an eye on more of the spectrum at the same time," Couture continues. "Ten years ago, technology would not have been able to pick out all the signals deep in the noise. But this also means the data becomes a bigger fire hose, so you will need multiple high-power processing to sort it all out."
The role of artificial intelligence
While advances in technology have occurred at a record pace in the past decade, experts say they will witness even greater speed and evolutionary technologies in the next decade and beyond that few can even partially predict. One that is on everyone's list, however, is artificial intelligence (AI), which is likely to play a major role in the future of EW.
"In the past in EW, you had a classified list of target signatures, but now there are more and more new threats and to counter some of them - especially if you are in theater in combat and seeing something for the first time - you have cognitive systems, a neural net AI, sometimes called deep learning or machine learning, to do this on the fly," Couture says. "It's in the toddler phase now, but these cognitive techniques will begin deploying in the next decade. This will require a lot more processing power than a decade ago. It used to be megaflops, now gigaflops, and becoming teraflops."
Today's processing challenge likely will require more than one kind of processing device, such as field-programmable gate arrays (FPGAs), general-purpose graphics processing units (GPGPUs), and advanced general-purpose processors (GPPs). "It will take a combination of two or more processors contributing what they do best to the EW technique," Couture says. "Everything also is getting faster, with multi-core processors and going from 10 to 40 to 100 gigabit Ethernet."
New techniques, such as swarming UAVs, are increasing the need for cognitive applications as a standard component of many, if not most, defense systems.
"When we think of technology advancing, we've tended to think of faster processors and GPUs with more cores, but while the underlying silicon enables a lot of advances, we are starting to code differently to enable far more sophisticated interconnected, correlated sensors," Couture says. "So it will be interesting to see what things look like in the next 10 to 20 years," he adds.
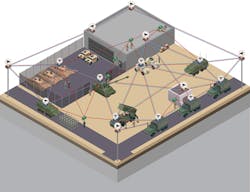
Adapting commercial off-the-shelf (COTS) technologies for secure military applications is, by itself, insufficient in today's evolving EW environment. More layers are required that neither interfere with, nor slow communications, across the wireless networks now linking all services and allied forces in the battlespace. An example of this is the small-form-factor Secure Wireless Command Post for forward operating bases from Pacific Star Communications Inc. (PacStar) in Portland, Ore.
Secure command post
The Secure Wireless Command Post system, based on the PacStar 400-Series modular platform, meets U.S. National Security Agency (NSA) Commercial Solutions for Classified (CSfC) Campus WLAN Capability Package v2.0 requirements and is customizable and configurable to meet other NSA CSfC capability package specifications.
End users have access to built-in commercial Wi-Fi on mobile devices to provide one layer of the required two-layer NSA encryption requirements, enabling warfighters to use commercial smartphones, tablet computers, and laptops to access classified information over Wi-Fi and LTE in deployed, expeditionary, and tactical environments.
"As computing gets more powerful and smaller, it has allowed the DOD to deploy more and more enterprise-class technology out to the network. But that can involve a huge system warfighters are not necessarily trained to use. So we integrate all those into a single system that is easier to use, burying a lot of enterprise items the warfighter doesn't need to interface with, but also making it easier for them to find and access those if they do need them," PacStar Chief Technology Officer Charlie Kawasaki explains.
"Through our management software, we automate and make simple the tasks that do need to be performed in the field and even cut across information technologies from different vendors, orchestrating the configuration under a single integrated user interface," Kawasaki says. "A rapidly deployable network infrastructure that is an enabler for any IP-based system at the edge of the battlespace, some of the components include an extensive implementation of wireless intrusion detection and prevention."
Part of the NSA requirement to field wireless is the ability to detect attacks over the Wi-Fi spectrum in a wide variety of forms, such as rogue access points and attempted connections into the infrastructure. Then the system must quarantine those potential threats, even flooding them with distributed denial-of-service (DDoS) attacks over the RF spectrum.
"As configured, our solution is not designed purposely as an offensive weapon; it is designed to maximally secure the system. But that isn't to say it can't be used for offense," Kawasaki adds. "If there is a proactive attempt to do something malicious to deny our forces access to a wireless network, then our system can take them down."
Evolving technologies
Future EW solutions also will take advantage of continuing evolutions in other technologies, especially the concept of deploying swarms of small UAVs linked across moving wireless mesh networks providing more than 100 megabits per second of usable bandwidth, UAV-to-UAV, enabling the sharing of fused sensor data, says Rajant Corp.'s Schena.
"We have a vision of applying our networking technology, which we already are doing to drone swarms, to create a wide-aperture lens over a battlespace that would allow the U.S. military to defeat an enemy's efforts in stealth technology," Schena says. "Our adversaries are moving quickly and investing as much in stealth as we have over the years. So while the U.S. hasn't had to face much stealth to date, it is coming. We are developing a technique to connect hundreds of drones and integrate hundreds of radar sets; we believe the analytics of that data will allow you to see platforms designed with stealth."
The next step is to create a coherent radar lens across a wide part of the battlespace, says Rajant Hardware Design Engineer Dave Grund. "As we connect these drones, we can form a very large aperture radar, communicating all this information through our network, to enable us to see things no one else can today," he says. "We could connect a large number of [radar-equipped UAVs] together in real time and gain a much greater level of information from different angles for analysis."
Schena says such a system could have a great impact on defensive EW, eliminating most of the advantages the enemy hopes to gain through stealth.
"We have a partnership with Moorehead State University in Kentucky, which has one of only five space and engineering programs in the country and is part of the deep-space network. Its students hand-build cubesats as part of their education and our next-generation plan includes moving our OS to small-scale satellites," Schena says.
"Where that is a defensive EW capability, if an adversary takes a shot at our GPS satellites, we can respond with a rapidly launched swarm of meshed satellites as a replacement - very little latency, highly effective, node-switching on the ground, in the air, and in the future, in space.
Don Gilbreath, Rajant's vice president of systems, points out that SWaP has become even more critical with the increasing demands on fielded technologies like EW. It is another area where the commercial market has taken the research lead, but military contractors must adopt and adapt those developments to support the Pentagon's growing demands.
"The more we looked at increasing numbers of units swarming in the air, we started looking at co-processing," Schena says. "But in any denied GPS environment, without miniaturization, we could never get to the level of horsepower needed to deal with that. The big bottleneck is the power source. Batteries, in terms of power density, really haven't gotten better in 25 years," he says, adding that much of today's commercial development is occurring outside the U.S.
"At the semiconductor level, some of the top-level components come from countries that may not be militarily friendly to the U.S," Schena says. "If you look at products coming out of Asia in recent years, we're seeing more wearable electronics. We clearly are doing more in localized distributed processing because communications is a lot more expensive and spectrum is limited."
"Secret operations are essential in war; upon them, the army relies to make its every move." - Sun Tzu
Ironically, while part of EW is the defense of classified information in the battlespace, other nations are using human and electronic spies to steal U.S. technology on a larger scale than perhaps at any other time in history. At the same time, most electronics are now being manufactured overseas. America's technology lead - with EW and other military systems - is in jeopardy.
"We're constantly surprised at what we find, both in the U.S. and internationally," Schena says. "We know our adversaries - even the biggest - are extremely sophisticated at stealing American technology, which greatly reduces the time gap between what we develop and when they match it. We still see a great deal of technology leadership in the U.S., but also growing capability globally and more and more theft of U.S. technology.
"With the resources available to us, both capital and human capital, we should be able to maintain our technology lead," Schena continues. "But our adversaries sometimes seem more focused on closing the gap than we are in maintaining it. In the past few decades, the U.S. has had such a profound lead in so many areas, especially the military, that we have come to believe that is the way it will always be."
Sierra Nevada Corp. has been one of the largest providers of small-form-factor EW technology across the DOD, with some 10,000 systems in the field, including the ALT-5 electronic RF countermeasure system, THOR II and III, and Baldr manpackable counter Radio-Controlled Improvised Explosive Device (RCIED) systems. Now they have made a significant departure from those legacy technologies with the Advanced EW System-Modular (AEWS-M).
"It is completely modular, mission-configurable, and all software-defined, ideally suited to provide offensive electronic attack, electronic defense, and electronic support capability, all within the same system. For example, counter-RCIED EW and counter-UAS," notes Sierra Nevada's Snyder.
"It is manpackable, but can be scaled up by adding auxiliary elements to connect to radar, additional amplifiers, and directional antennas, Snyder says. "This makes it a much more expandable capability, based on mission requirements. Because of its modularity, it also is ideally suited for vehicles or aircraft. The AEWS-M is already fielded and deployed worldwide, but I can't identify the customer."
Manpackable EW
The new AEWS-M's provenance also demonstrates a change in how industry is taking a more autonomous approach to evolving EW and related technologies through independent research and development (IRAD).
"This wasn't driven so much by government requirements as understanding the environment at large, so a lot of our work is done on IRAD, aligning with where the military is trying to go. They used to have a lot of set pieces providing a single function, which raised SWaP issues. Now you have to provide a capability that is adaptable to current and future environments to deal with all threats in the spectral domain," Snyder explains. "The spectrum is finite and contained for now, but you must have the ability to expand your frequency range going forward.
"You need a foundation in your architecture that allows continued expansion to maintain the relevancy of your technologies," Snyder says. "If you cannot quickly adapt to an adversary, you will not maintain relevance against the threat. That's why systems are becoming software-defined, to dynamically support program changes. You have to be spectrally aware and robust, so you're looking at as much relevant spectrum as possible to understand what is going on around you and adapt to it quickly."
That means moving from fixed architectures to more ad-hoc mesh capabilities. A primary part of the EW design is disruption of communications. For those architectures to stay alive, they must be self-healing and not so fragile that disrupting one part brings the whole network down.
"You need an amazing amount of resources and agility. Counter-measures are the trade space going forward, the key spaces. You don't necessarily focus on jammer versus jammer, but on my spectral integrity versus your spectral integrity, pairing EW capabilities against an adversary's spectrum. The enemy's jammer won't necessarily be defeated; you harden against it or find ways to mitigate its effects, but you don't build EW tech to squarely go against EW tech," Snyder says.
"You may have great weapons, but without vehicles to maneuver about the battlespace, you can't win. That also applies to EW," Snyder adds. "Not dominating the battlespace will reduce your communications capability, which, holistically, degrades your overall capability. Our tech is warfighter-focused and we are evolving it to meet what the warfighters need, when, where, and how they need it - a small-form-factor, multifunction, mission-configurable, system-of-systems EW design that can be used by an EW specialist, a cook, a scout, or anyone, which is critical at the edge of the battlefield."