iWar
Technology companies devise innovations to help combat the growing threat of information warfare.
By Courtney E. Howard
“Hostile actions against an enemy’s information infrastructure” reads the description of “infowar,” a new addition to The Oxford Pocket Dictionary of Current English. The terminology, often shortened even further to “iWar,” may be new, but the practice certainly is not.
Information warfare can take many forms: virus, malware, and spyware attacks; trojans and worms; stolen laptops, thumb drives, and iPods; and so on. Security breaches at individual and enterprise levels can have dire consequences, but those at a military and federal level can be catastrophic.
Technological terrorism
Terrorists are using the Internet as a vehicle for attacking national infrastructure, using bytes rather than bombs. Hacking tools have been found on the computers of known members of Al Qaeda, in fact. Al Qaeda and other organizations and governments are known to be engaging in and advancing their information-warfare tactics and doing reconnaissance on U.S. computer networks and critical infrastructure. It is now possible for someone sitting in a cybercafé virtually anywhere to precisely locate a target country’s natural gas repositories, railroad crossings and bridges, and much, much more.
Richard Clarke—who has previously held the positions of chief counter-terrorism adviser the U.S. National Security Council, presidential adviser for Cyberspace Security, and member of the Senior Executive Service specializing in intelligence, cyber security, and counter-terrorism—has described these findings as very troubling.
Modern national powers such as the U.S., once built only on brick and mortar, now largely depend upon bits and bytes. Economies and militaries are increasingly cyber-based, and therefore susceptible to hostile organizations known to be growing their cyber-warfare capabilities. The fear, Clarke has explained, is that these empires are being built on a fragile base that, if goes unsecured and fortified, can and will one day be toppled.
Ensuring the security of critical information is a key aim and high priority of today’s military organizations, as well as the technology companies that serve them. Government and industry are working in tandem to thwart information warfare, while enabling military personnel to gather, gain secure access to, covertly transmit, and protect critical information.
Securing netcentricity
A network-centric battlefield, in which “the right people get the right information at the right time,” is the future. The exchange of sensitive and even top-secret data is integral to this network-centric vision of the U.S. Department of Defense. Netcentricity makes mission-critical information available to a larger number of military personnel; yet, it may also provide cyber-terrorists with greater opportunities to access important data. Military networks—classified (SIPRNET) and unclassified (NIPRNET)—must be secure, and data exchange and access continually protected.
“Accurate up-to-date information is critical to the defense of any country,” acknowledges Robert Hoffman, vice president and general manager of Aerospace and Defense at Wind River in Alameda, Calif. “From the individual warfighter to large-scale theaters to worldwide military planning and execution, rapid secure communication is critical to lethality and survivability.”
Information warfare in a net-centric battlefield can take many forms—whether interference with communications (jamming, denial of information collection and dissemination), interference with information validity (corruption of friendly force information or insertion of opposing force disinformation), or unauthorized information release (leakage)—and all are continuous and growing threats to national security, continues Hoffman.
Every warfighter is a node on the net-centric battlefield, and therefore must be outfitted with various electronic systems, ranging from sensors to handheld computers or other communication devices. Size, weight, and power (SWaP) are major concerns when it comes to soldier-borne electronic systems, which can also pose a security problem.
“A special challenge to information assurance arises from the compelling need to increase the functionality of defense systems while reducing their space, weight, and power,” Hoffman mentions. “Meeting this demand requires co-mingling information from different sources, possibly at different classification levels or from different coalition partners more closely than in the past, yet still with separation as required.”
New system architectures that satisfy SWaP demands and offer the high assurance of information security are emerging. Multiple Independent Levels of Security (MILS) is such a system.
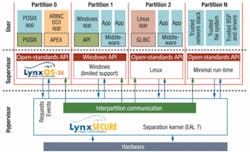
“The MILS architecture permits multiple user components (applications, middleware, drivers), each with their own security requirements, to be co-resident on a single processor,” Hoffman explains. The MILS architecture, describes Hoffman, has three layers: trusted hardware; a separation kernel responsible for data isolation, periods processing, information flow control, and fault isolation, running in “supervisor mode;” and a number of user components running in user-mode partitions. The separation kernel and other security-critical elements—such as minimal partition runtime to support high-assurance applications, trusted stack, etc.—are evaluated and certified using the international Common Criteria for Information Technology Security Evaluation, a methodology that at the highest levels includes mathematical proof elements for very high assurance.
“The MILS architecture, with its inherent capabilities to support highly secure systems and reduce cost for development, certification, and long-term cost-of-change, will see use in a growing number of defense systems and also systems outside defense, such as energy generation and distribution, first-responder systems, industrial systems, medical instrumentation, and even financial systems,” Hoffman predicts. In fact, Wind River’s VxWorks MILS Platform has been selected for systems requiring multilevel security, but which are either classified, subject to U.S. International Traffic in Arms Regulations (ITAR), or competition sensitive, and cannot be revealed.
Sharing information
“If knowledge is power, then protecting our digital rights is paramount to maintaining our freedoms and way of life,” says Steve Blackman, director of mil/aero business development at LynuxWorks in San Jose, Calif. From a military perspective, the protection of sensitive information has always been a critical need, he explains.
“Decades ago, in search of safer software, the concept of the separation kernel was born,” Blackman recalls. “The idea is that if one can create a large number of small virtual enclaves, then the amount of risk each enclave bears is similarly reduced. At the same time, the complexity and size of the reference monitor of these enclaves is reduced to the point that the software can and has been developed with trust.” The resulting MILS architecture, he says, has been promoted as a superior approach to create a commercial off-the-shelf and standards-based infrastructure to enable end-to-end, secure information sharing on the global information grid (GIG).
Information sharing is central to the success of the network-centric vision. The network-centric battlefield makes information available worldwide on a 24x7 basis. It does so, however, not only to soldiers and allies, but also to enemies, terrorists, and hackers, making the risks greater and protection more challenging, Blackman admits. “As systems become more complex and multifunctional, different levels of information security need to be handled by a single system, which then adds additional complications for designing the software to provide access to this information.”
Companies such as LynuxWorks are delivering technologies for building medium- and high-assurance network solutions that provide trusted separation of different security domains on a single computer system. These technologies enable the sharing of secure information across multiple domains on a single computer, and support multilevel information in a single computer or network of computers.
“These solutions are being evaluated and accredited by government agencies and representatives to address the information-assurance requirements for the environments in which these systems will operate,” describes Blackman. “The information-assurance requirements are defined in protection profiles and describe in detail all the requirements to assure the system is protected for all the information assurance-related risks, including hackers and terrorist attacks.”
It starts, Blackman continues, with mandatory access controls (MAC) and extends to more sophisticated protections against intrusions; for example, running the OS software at system level with all other middleware, device drivers, and application software at user level to prevent unauthorized access to system resources (devices, memory, CPU time, I/O), along with constant monitoring of all the functions running to insure and enforce they are only doing what they are authorized to do and accessing only the resources to which they are privileged.
LynuxWorks delivers medium-assurance solutions, having a Common Criteria Evaluation Assurance Level of 4+ (EAL4+), and high-assurance (EAL6+) tools. LynxOS-SE, a medium-assurance solution, is being used by the U.S. Army’s Future Combat Systems and will be evaluated/certified for this program. LynxSecure, a high-assurance solution using Intel’s VT (Virtualization Technology), is being evaluated and utilized in IRAD (internal research and development) projects of many defense contractors in the U.S.
Technology firms continue to advance their solutions, enabling users to take full advantage of the latest hardware and software innovations. LynuxWorks’ LynxSecure symmetric multiprocessing (SMP)-capable separation kernel/hypervisor, for example, supports multicore CPU (central processing unit) architectures, which continue to grow in popularity and adoption, displacing legacy systems where appropriate.
A hypervisor is a virtualization platform that enables multiple operating systems, and their applications, to run on a single host computer simultaneously. Hypervisors and virtualization technology are well suited to mil-aero applications, as they can offer significant size, weight, power, and cost (SWaP-C) savings through hardware consolidation. Companies such as Green Hills Software and LynuxWorks are delivering this technology, combined with a secure real-time operating system (RTOS), to the mil-aero market.
In a single processor, the hypervisor allocates a virtual CPU to each partition, and the real CPU is used as a cache for the virtual CPU when a partition is running, Blackman explains. In a true multicore system, more real CPUs act as caches for virtual CPUs simultaneously.
Today’s threats
Whereas industry firms are harnessing new hardware and software to enable novel systems in which information is well protected, many military platforms sport older, legacy systems ill equipped to thwart information-warfare attempts.
“The global information grid is creating large, connected computer worlds running legacy operating environments (Windows, Linux, VMware) that were simply not designed for high assurance, and can’t meet the security requirements for sensitive information handling,” says David Kleidermacher, chief technology officer of Green Hills Software Inc. in Santa Barbara, Calif.
Companies such as Green Hills are working with leading defense contractors, OEMs, and end users to improve the security technologies and policies involved in information warfare. In fact, Green Hills’ Integrity RTOS has been accepted into a high-robustness Common Criteria (EAL 6+) security evaluation, “providing mathematical proof of security,” says Kleidermacher. The software has been adopted by the F-35 Joint Strike Fighter and the Boeing 787 Dreamliner flight control system, and it is found in military information systems, “approved by the National Security Agency (NSA) for protecting the most sensitive national secrets.”
Green Hills’ Integrity is used throughout the Joint Tactical Radio System (JTRS) program, by such industry players as Boeing in Chicago. In one project, explains Kleidermacher, Boeing engineers use Integrity and Green Hills Software’s Padded Cell secure hypervisor to concurrently run a Linux system alongside critical applications running directly on Integrity. Padded Cell technology implements a virtual computer in a user-mode application running on top of Integrity. Multiple Padded Cell applications can run concurrently on a single computer and each host its own guest operating system. “An impenetrable wall around each virtual computer ensures that errant, insecure, or malicious code can never compromise the security or reliability of the rest of the system—either inadvertently or via a hostile attack,” says a company representative.
Global importance
“The next large global conflicts will be unlike anything we’ve seen before, and information warfare will be a large—perhaps defining—component,” says John Keller, chief editor of Military & Aerospace Electronics (see “The importance of military information security,” in the October 2007 print issue of Military & Aerospace Electronics). “Make no mistake; information security is one of the most important military issues of the 21st century.”
It is a major area of activity across the world, notes Blackman. “The requirements for increased information security extend to Europe/Asia and the Middle East.” As a result, he predicts the future availability of many more component- and system-level solutions to address security and to prevent reverse engineering of technologies. “Most will be built on a MILS architecture,” he says, “which enables faster certification/accreditation and lower long-term costs for high-assurance systems. There will also be close relationships between the hardware and software companies and platforms that will enable the underlying separation technology for developing MILS solutions.”
The computer and the data network will be the aircraft carrier and atomic bomb of the future, Keller offers. “If a nation can exploit its enemies’ computers and data networks, then it clearly has the upper hand. Conversely, a nation that cannot safeguard its own computers and data networks has little chance of prevailing.”
VMware gains security certification, meets government standards
VMware Infrastructure 3, VMware ESX Server 3.0.2, and VMware VirtualCenter 2.0.2 from VMware Inc., maker of virtualization solutions in Palo Alto, Calif., earned Common Criteria Evaluation Assurance Level 4 (EAL4+) certification under the Communications Security Establishment Canada (CSEC) Common Criteria Evaluation and Certification Scheme (CCS).
“Passing this rigorous, globally recognized certification process demonstrates our commitment to delivering secure, reliable virtualization products,” says Dr. Stephen Herrod, chief technology officer for VMware. VMware Infrastructure, he continues, “can be used not just for commercial computing, but for sensitive, government computing environments that demand the strictest security.”
Among VMware’s customers are many government agencies, including all 15 cabinet-level agencies, all branches of the military, and the Department of Defense Joint Commands.
Common Criteria is an internationally recognized set of guidelines (ISO 15408) that define a common framework for evaluating security features and capabilities of Information Technology security products, describes a representative. The standard consists of several predetermined evaluation assurance levels.
Common Criteria certifications are accepted by 25 countries, including the U.S. government, through the Common Criteria Recognition Agreement (CCRA). Common Criteria certification of security products is mandated by the U.S. government for all federal purchases.
For more information, visit VMware online at www.vmware.com.
General Dynamics safeguards sensitive data with GuardianEdge
General Dynamics, headquartered in Falls Church, Va., is protecting sensitive U.S. Department of Defense information and customer data on company laptops and removable storage devices with GuardianEdge’s Device Control and Removable Storage Encryption solutions.
General Dynamics serves customers, such as government agencies and other organizations charged with ensuring national security and military operations, in business aviation; land and expeditionary combat systems, armaments, and munitions; shipbuilding and marine systems; and information systems and technologies.
GuardianEdge enables General Dynamics officials to secure company laptops and removable storage devices by preventing the transfer of sensitive or confidential data to unauthorized devices, such as iPods, CDs, DVDs, and USB thumb drives, and by ensuring the data is encrypted.
“Many of our customers work directly on matters of national security,” says Ram Krishnan, senior vice president of products and marketing at GuardianEdge. “In the event a laptop or removable storage device is lost or stolen, it is critical that we enable them to demonstrate that the intellectual property contained on that device is secure. GuardianEdge helps General Dynamics address data security concerns and meet strict internal security requirements through a comprehensive set of solutions that deliver strong, centrally managed data protection.”
To safeguard against data leakage, GuardianEdge Device Control prevents the unauthorized transfer of data from corporate PCs by restricting user access to external devices and ports with centralized policies.
GuardianEdge Removable Storage Encryption enforces the encryption of critical information upon transfer to removable media devices or formats.
By combining these two solutions, General Dynamics officials prevent data transfer to unauthorized devices and ensure transferred data is protected via encryption in case a device is lost or stolen.
For additional information about these solutions, visit GuardianEdge online at www.guardianedge.com.