The need for trusted data storage
Keeping crucial mission data safe and out of the enemy's hands requires trusted memory chips, reliable encryption, and anti-tamper technology to foil prying hands.
The ability to store data is crucial for a wide variety of military systems - particularly for sensor, surveillance and reconnaissance, signals intelligence (SIGINT), electronic warfare (EW), and many other applications. Yet perhaps as important as storing the data is the ability to trust and safeguard this data once it's written onto storage media like solid-state drives.
The big question is how to design-in trusted data storage that is secure from attempts to steal, disrupt, or tamper with the data and the storage media onto which applications write it. Adversaries of U.S. and allied military forces pose a bigger threat to stored data today than ever before, and the threat is growing daily.
The VP1-250-SSDC VPX storage module from Phoenix International supports AES-256 and FIPS 140-2 data encryption.
Government authorities, systems integrators, and data storage vendors today have come up with several ways to safeguard stored data, ranging from security at the chip level, several different levels of progressively stringent encryption, anti-tamper measures, and other approaches to keep data safe, accurate, and trusted.
With increasing frequency, military systems integrators and the military services require specific levels of trust in data storage; it's rarely an option anymore to offer data storage for military applications without appropriate levels of security. "Not everything requires security today, but more and more the trend is to have data secured," says Amos Deacon III, president of data storage specialist Phoenix International Systems in Orange, Calif.
At issue is the growing number of platforms like unmanned aerial vehicles (UAVs) that have substantial amounts of sensitive data aboard. Military leaders want to ensure that adversaries cannot gain access to this data by any means, especially should an unmanned aircraft be shot down or otherwise captured by the enemy.
"We are certainly seeing more and more applications that are requiring security for data at rest - especially with the increase in unmanned vehicles in the air, on land, and underwater," says Paul Davis, director of product management at the Curtiss-Wright Corp. Defense Solutions Division in Dayton, Ohio.
Trusted memory chips
With few exceptions, data storage for aerospace and defense applications today relies on solid-state memory, for its advantages in speed, size, and reliability in harsh operating environments. Typical memory chips are NAND Flash memory, either single-level cell (SLC) or multi-level cell (MLC). Triple-level cell (TLC) Flash memory chips are becoming available, and eventually quad-level cell (QLC) Flash memory will enter the market.
From this standpoint, trusted data storage starts with trusted solid-state memory chips. Trusted memory specialist Mercury Systems in Phoenix uses memory chips accredited by the U.S. Defense Microelectronics Activity (DMEA) in McClellan, Calif., near Sacramento.
"Accreditation to the DMEA Trusted Foundry program is to assure integrity and confidentiality of integrated circuits during design and manufacturing," explains Bob Lazaravich, Mercury's technical director for secure storage. "Very few manufacturers in our space are on that DMEA list."
The Phalanx II rugged network attached storage (NAS) system from Phoenix International has hot-swappable, solid-state drives supports AES-256 and FIPS 140-2 data encryption.
The program also helps provide the U.S. government with access to leading-edge microelectronics technologies for trusted and non-sensitive applications. Trusted describes confidence in one's ability to secure national security systems by assessing the integrity of the people and processes involved in the design, generation, manufacturing, and distribution of components critical to national security.
DMEA Trusted Foundry accred-itation for Mercury's memory chip manufacturing facility in Phoenix provides an assured chain of custody for classified and unclassified integrated circuits (ICs); ensures there will not be reasonable threats related to chip disruption in supply; prevents intentional or unintentional modification or tampering of the ICs; and protects the ICs from unauthorized attempts at reverse engineering, exposure of functionality, or evaluation of their possible vulnerabilities.
In addition to accredited chip manufacturing, Mercury's Lazaravich recommends maintaining the intellectual property (IP) related to NAND Flash processors and controllers. "That way you are in full control of the security implementation right down to the source code," he says.
"Commercial systems go end-of-life every few years, and defense integrators want a system that will last for many years," Lazaravich continues. "If you own the IP, it enables you to add custom features that customers want. A commercial processor offers no chance to do that."
Layers of encryption
Encryption for data storage comes in several different levels of security, spelled out in standards from international authorities; the U.S. Department of Defense's National Security Agency (NSA) at Fort Mead, Md.; and the U.S. Department of Commerce National Institute of Standards and Technology (NIST) in Gaithersburg, Md.
Perhaps the most accessible commercial encryption standards are the Security Requirements for Cryptographic Modules standard, outlined in Federal Information Processing Standard (FIPS) 140-2; and the Advanced Encryption Standards (AES), outlined in FIPS 197. These commercial-level encryption standards are administered by NIST.
FIPS 140-2 is a U.S. government computer security standard to coordinate the requirements and standards for approving cryptographic modules that maintain the confidentiality and integrity of encrypted information.
The Mission-Stor solid-state drive from Mercury Systems is a military-grade, handheld storage device with integrated security. The device is similar in size to a commercial-grade USB memory thumb drive, and offers FIPS 140-2 and CSfC encryption.
The standard provides four increasing levels of security, and covers areas, such as: module specification; ports and interfaces; roles, services, and authentication; physical security; operational environment; cryptographic key management; electromagnetic interference; self-test; design assurance; and mitigation of other attacks.
FIPS 140-2 defines four levels of security. Level 1, the lowest level of security, involves a cryptographic algorithm, but no physical security mechanisms. Level 2 includes features that show evidence of tampering. Level 3 attempts to prevent an intruder from gaining access to cryptographic keys. Level 4, the standard's highest level of security, calls for physical security mechanisms to detect and respond to all unauthorized attempts at physical access.
"If our customers don't need NAS review and approval, then there are products out there using commercial encryption," says Curtiss-Wright's Davis. "We have products that incorporate FIPS 140-2 encryptors." He calls FIPS 140-2 "an inch wide and a mile deep," because it studies the encryption very deeply, but only the encryption.
The AES, meanwhile, specifies a FIPS-approved cryptographic algorithm that is a symmetric block cipher that can encrypt and decrypt information. It can use cryptographic keys of 128, 192, and 256 bits to encrypt and decrypt data in blocks of 128 bits.
"Just about everybody uses AES-256 encryption," says Phoenix Inter-national's Deacon. "It has been ac-cepted as sufficient that it would take all the supercomputers in the world hundreds of years to brute-force your way into it." Phoenix designers use AES-certified solid-state drives from authorized drive vendors on several of the company's products.
"We are seeing another layer of protection, the FIPS 140 levels, typically in addition to AES-256 electronic encryption," Deacon says. FIPS 140 typically is called into use for systems that require some physical protection of the drive. "If somebody tries to open a disk, you can tell. We are seeing that FIPS 140-2 requirement more and more these days."
International encryption standards
An increasingly popular encryption approach on the international front is the Common Criteria for Information Technology Security Evaluation, administered by the NSA's National Information Assurance Partnership (NIAP).
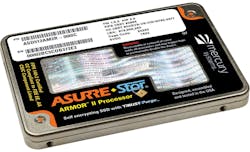
The ASURRE-Stor self-encrypting, solid-state drive from Mercury Systems blends high-endurance NAND flash with a military-hardened 2.5-inch form factor and CSfC encryption.
Common Criteria is a technically demanding international set of guidelines for security certification recognized by the U.S. and 27 other governments worldwide for protecting sensitive stored data. It provides assurance that the process of specification, implementation, and evaluation happens in a rigorous, standard, and repeatable manner.
The Common Criteria enables data storage users to specify their security and assurance requirements, and provides a means for data storage vendors to design in these security attributes. Authorized testing laboratories then evaluate the products to determine if they actually meet requirements.
"The Common Criteria is a mile wide and an inch deep," says Curtiss-Wright's Davis. "They expect you to use FIPS-certified encryption, and they are concerned with how you use it and how you access the system data; it's a very exhaustive examination of your system. You could have the best encryption in the world, but if your password were silly someone could access it. The system needs to be set up properly, and the Common Criteria looks at the whole system."
Curtiss-Wright has begun the Common Criteria certification process for the company's Data Transport System (DTS1) network attached single-slot data recorder, which is being evaluated by Gossamer Security Solutions Inc. in Catonsville, Md.
The Curtiss-Wright DTS1 network-attached storage device is designed to store and protect large amounts of data on helicopters; unmanned aircraft, underwater vehicles, and ground vehicles; and on manned intelligence, surveillance, and reconnaissance aircraft that must protect sensitive information.
The DTS1 offers as much as two terabytes of solid-state storage for military aircraft or ground vehicle applications. The VS-DTS1SL-FD is designed for use with DZUS chassis, and the VSDTS1SL-F uses L-brackets to support mounting within space-constrained areas.
NSA-certified encryption
Common Criteria certification also is one of the first steps toward implementing the NSA's Commercial Solutions for Classified (CSfC) two-layer encryption for protecting classified information in aerospace and defense applications.
CSfC is intended to be a cost-effective way to use layered commercial encryption technologies in trusted data storage. The NSA has established the CSfC program as an alternative to the agency's more-stringent and more expensive Type 1 encryption.
NSA officials developed the CSfC program to deliver secure solutions using commercial encryption to get trusted data solutions to industry quickly. It works on the assumption that properly configured, layered solutions can provide adequate protection of classified data in selected applications.
The Data Transport System (DTS1) network-attached data storage system from Curtiss-Wright is undergoing evaluation for the international Common Criteria encryption standard for handling classified data.
The CSfC program enables systems designers to use commercial products in layered solutions to protect classified data in a solution that can be fielded in months, not years. It's been described as two pieces of Swiss cheese - each with identical holes. Rotate one piece 90 degrees, however, and most, if not all, of the holes are covered.
"I'm seeing CSfC gain acceptance in military programs," says Steve Edwards, director of secure embedded solutions at the Curtiss-Wright Defense Solutions headquarters in Ashburn, Va. "We have a customer that has asked us to apply these two levels of CSfC encryption on a UAV. The commercial approach overall is less expensive, and the approach we are taking is cost savings for the customer."
The most demanding encryption available for trusted data storage is NSA Type 1, which is an encryption device or system certified by the NSA for use in securing classified military or other government information. It's expensive and time-consuming to implement, and Type 1-certified encryptors are available only from a handful of certified providers. Type 1 certification is a rigorous process that includes testing and formal analysis of cryptographic security, functional security, tamper resistance, emissions security, and security of the product manufacturing and distribution process.
Anti-tamper
Secure data storage needs more than just encryption to safeguard information properly. Security experts particularly are interested in denying an adversary physical access to data drives if systems fall into the wrong hands. "In addition to the data being encrypted, they want to see if someone has tried to get in," says Phoenix International's Deacon.
Encryption "does very little to prevent tampering from an attacker," adds Mercury's Lazaravich. "We use active and passive sensors to determine if something is happening to the enclosure or the system. No two customers want the same thing."
Anti-tamper technology is intended to prevent not only unauthorized access to stored data, but also to keep an adversary from reverse-engineering data drives or storage systems. "There is a need for self-destruct," says Mercury's Lazaravich. "What happens in self-destruct is one or more component swill be physically destroyed, and the firmware is erased to make the system useless."
Anti-tamper mechanisms come in several different layers, beginning with the automatic erasing of encryption keys if the system detects attempts at unauthorized access. "If somebody is trying to get hold of the data you need to protect, then I have an appropriate response like deleting the encryption key. That's a common approach," says Curtiss-Wright's Edwards.
Erasing a storage drive's encryption key makes decryption impossible, rendering the data essentially into gibberish. "There is no way to recover that key," says Curtiss-Wright's Davis. "That is one of the other benefits of two-layer encryption: you have two sets of keys."
Different approaches also may involve quickly erasing the stored data, as well as physically destroying the memory chips themselves. Erasing the data reliably, however, can take too much time - an hour or so, which often isn't available.
"Typically, you do not try to erase the data because that takes a long time," Edwards says. "You can erase an encryption key almost instantaneously."
Some approaches call for the physical destruction of the data storage medium if it detects attempts at unauthorized access.
"Mercury solid-state drives have a no-power self-destruct feature so that the drive can be destroyed in a fraction of a second with a mechanical mechanism that destroys an integrated circuit on the inside with magnetic fields," Lazaravich says. "It's a nice way to do a destruct and get rid of data with no remnants."
This process can involve physically burning-out memory chips.
"A solid-state disk can electronically burn-out the memory chips so they are unusable," says Phoenix International's Deacon. "Typically, there are a couple of pins designated to do that, and can short-out the memory chips so they are unusable."