Zero trust gains momentum in U.S. military's new approach to managing microelectronics acquisition
WASHINGTON – Zero trust architecture is becoming more popular in the U.S. Department of Defense (DOD) and serves as a model for how the military fields microelectronics. Fedscoop reports. Continue reading original article
The Military & Aerospace Electronics take:
17 June 2020 -- Zero trust security relies on continuous validation for access as a user moves around a network regardless of his physical location and relationship to an organization, instead of a one-and-done security check like the normal user name and password. In essence, it gives users or other device personas accessing a network “zero trust” as it connects to a network.
That mentality is the leading force behind how the DOD performs microelectronics acquisition, says Mark Lewis, director of defense research and engineering for modernization.
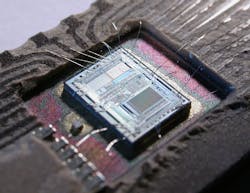
Microelectronics are in everything from weapons systems on fighter jets to IT platforms. If a malicious or weak microchip is implanted into the military’s systems, it could open wide cyber attack options. Zero trust is the department’s new answer to replace the older “trusted foundry” system where DOD had oversight over the physical development of the microelectronics.
Related: Are we in the midst of an embedded computing industry shakeout?
John Keller, chief editor
Military & Aerospace Electronics